Crypto Key Generate Rsa Modulus 360
- Crypto Key Generate Rsa Modulus 360 Price
- Openssl Rsa Modulus
- Crypto Key Generate Rsa 1024
- Crypto Key Generate Rsa Modulus 360 Review
- Cisco Crypto Key Generate Rsa
- Crypto Key Generate Rsa Command
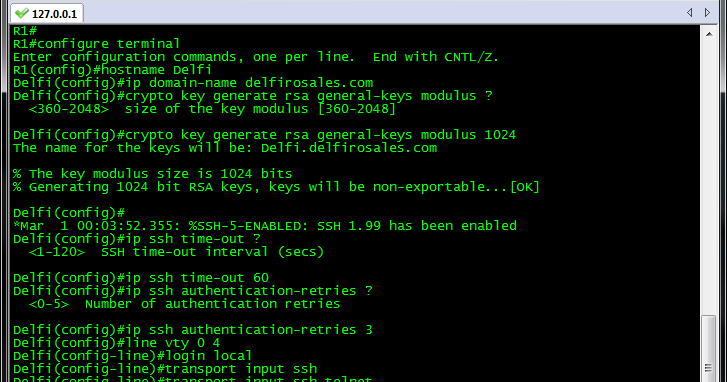
How I create RSA key and enable SSH access in Cisco VG202, in a Cisco router I use the next commands(but in a VG not exists): conf t crypto key generate rsa modulus 1024 ip domain-name domain-name ip ssh version 2 ip ssh time-out 120 ip ssh. R1(config)# crypto key generate rsa The name for the keys will be: R1.firewall.cx Choose the size of the key modulus in the range of 360 to 4096 for your General Purpose Keys. Choosing a key modulus greater than 512 may take a few minutes. How many bits in the modulus 512: 4096% Generating 4096 bit RSA keys, keys will be non-exportable. End with CNTL/Z. Router1(config)#crypto key generate rsa The name for the keys will be: Router1.oreilly.com Choose the size of the key modulus in the range of 360 to 2048 for your General Purpose Keys. Choosing a key modulus greater than 512 may take a few minutes. How many bits in the modulus 512: 1024 Generating RSA keys.
Crypto Key Generate Rsa Modulus 360 Price
When it comes to device management you want to ensure that the traffic is secure and encrypted. Telnet unfortunately is not encrypted which is why SSH is commonly used for administration of Cisco devices. This lab will discuss and demonstrate the configuration of SSH v1.99 (v2)
Real World Application
Telnet just does not cut the cheese anymore when it comes to production network remote administration security. As you may be aware, telnet does not encrypt the encapsulated payload so with that being said; anyone on the wire can sniff the traffic and reconstruct the telnet communications which opens a major vulnerability that passwords can be sniffed as well as other types of confidential sensitive information that traverses a network via the telnet protocol.
This has been a known issue since the birth of Telnet and has been resolved with the introduction of Secure Shell, also known as SSH.
SSH in a nut shell is basically Telnet using encryption to securely encapsulate the traffic payload to prevent unwanted sniffing of such traffic. SSH can use different types of encryption algorithms from Data Encryption Standard (DES) all the way up to AES 256Bit CBC.
Lab Prerequisites
- If you are using GNS3 than load the Free CCNA Workbook GNS3 topology and start R1.
- Establish a console session with Router 1.
- Create a loopback interface and configure it with the IP Address 10.1.1.1/24
- Create an arbitrary username and password in the local user database as required by SSH in order for the VTY lines to establish a remote exec session.
- The VTY Line(s) authentication should be configured to authenticate to the local database. (Note that you can use login local or a AAA authentication list to accomplish this)
Lab Objectives
- Change the hostname from its default hostname Router to something specific to the device. ie; R1
- To generate an RSA key, you’re required to have a domain name set. Set the domain name executing the ip domain-name domainname.net command in global configuration.
- Create an RSA Genera-Usage certification that is self-signed by the Cisco device.
- Configure the transport input protocol on the VTY lines to only accept SSH (this disables telnet and permits only ssh)
Lab Instruction
Step 1. As a requirement to generate an RSA general-usage key you’ll need to change the hostname to a hostname other then the default “Router” hostname. In this case, you can use R1 as shown below;
Openssl Rsa Modulus
Step 2. Another requirement prior to generating an RSA certificate on the Cisco device is to set a domain name. For the purposes of this lab, the domain name will be set to freeccnaworkbook.com as shown below;
Step 3. Now you’re ready to generate the RSA certificate. To generate the RSA certification you’ll execute the crypto key generate rsa general-keys modulus command followed by the modulus keysize which ranges between [360-2048]. As shown below, an RSA certificate is generated using a 1024 bit modulus key.
Crypto Key Generate Rsa 1024
You’ll notice that immediately after the RSA General use keys are generated, SSH v1.99 is enabled. Note that the larger the keysize, the longer it takes to generate.
Once SSH v1.99 is enabled you can connect to the Cisco device remotely using the SSH v2 protocol found in Putty, SecureCRT and other terminal emulators; excluding HyperTerminal as it does not support cryptographic connectivity.
Step 5. Configure the transport input protocol on the VTY lines to accept only SSH by executing the transport input ssh under the vty line configuration mode as shown below;
/generate-ssh-key-terminal-ubuntu.html. Step 6. Verify your SSH configuration by using the Cisco IOS SSH client and SSH to the routers loopback interface 10.1.1.1
Minimal documentation regarding the Cisco IOS SSH client exist. Use the Cisco IOS context help ? to view available ssh command options.
RSA(Rivest-Shamir-Adleman) is an Asymmetric encryption technique that uses two different keys as public and private keys to perform the encryption and decryption. With RSA, you can encrypt sensitive information with a public key and a matching private key is used to decrypt the encrypted message. Asymmetric encryption is mostly used when there are 2 different endpoints are involved such as VPN client and server, SSH, etc.
Below is an online tool to perform RSA encryption and decryption as a RSA calculator.
For Java implementation of RSA, you can follow this article.
First, we require public and private keys for RSA encryption and decryption. Hence, below is the tool to generate RSA key online. It generates RSA public key as well as the private key of size 512 bit, 1024 bit, 2048 bit, 3072 bit and 4096 bit with Base64 encoded.
By default, the private key is generated in PKCS#8 format and the public key is generated in X.509 format.
Generate RSA Key Online
Public Key
RSA Encryption and Decryption Online
Below is the tool for encryption and decryption. Either you can use the public/private keys generated above or supply your own public/private keys.
Any private or public key value that you enter or we generate is not stored on this site, this tool is provided via an HTTPS URL to ensure that private keys cannot be stolen.
This tool provides flexibility for RSA encrypt with public key as well as private key along with RSA decrypt with public or private key.
If You Appreciate What We Do Here On Devglan, You Can Consider:
- Like us at: or follow us at
- Share this article on social media or with your teammates.
- We are thankful for your never ending support.
Usage Guide - RSA Encryption and Decryption Online
In the first section of this tool, you can generate public or private keys. To do so, select the RSA key size among 515, 1024, 2048 and 4096 bit click on the button. This will generate the keys for you.
For encryption and decryption, enter the plain text and supply the key. As the encryption can be done using both the keys, you need to tell the tool about the key type that you have supplied with the help of radio button. By default, public key is selected. Then, you can use the cipher type to be used for the encryption. The different cipger options are RSA, RSA/ECB/PKCS1Padding and RSA/ECB/OAEPWithSHA-1AndMGF1Padding. Now, once you click the encrypt button the encrypted result will be shown in the textarea just below the button.
Remember, the encrypted result is by default base64 encoded.
Similarly, for decryption the process is same. Here, you need to enter the RSA encrypted text and the result will be a plain-text. You have both options to decrypt the encryption with public and private keys.
Crypto Key Generate Rsa Modulus 360 Review
References